Risk Assessment Report
Risk assessment is the process conducted by an organization to identify and analyze the risks that are likely to occur in the organization. The identification and analysis of risks help organizations to implement measures that can help mitigate the risks. There are different steps involved in the risk assessment process. The initial step involves the identification of possible threats likely to affect the organization. The next stage includes noting the possible targets of the identified risks. Possible targets can include network users or even network resources. The organization then proceeds to rate the different identified risks according to their possibility of occurring and their impact in case they occur. Different mitigation measures are then developed and implemented, beginning with the highly prioritized risks. The different fields that makeup risk assessment in an organization include risk analysis, risk mitigation, and risk management (Anikin, 2015).
Would you like an authentic copy of “Risk Assessment Report “? Get in touch with us.
Risk Analysis
Risks refer to threats that have not yet been implemented or occurred in an organization. The identification of risks is conducted through vulnerability and threat assessments. Risk management and analysis are done by identifying threats that can affect the organization, grouping the risks into categories based on the probability of their occurrence, and implementing measures to address the identified risks (Behnia et al., 2012). Risk comprises the presence of an asset, a vulnerability, and the availability of a threat. The asset refers to any network component owned by the organization, and vulnerabilities refer to the security flaws a threat can easily exploit. A threat refers to someone who can identify the vulnerabilities in a system and use them to cause harm to the system. A threat can also refer to something that can accidentally cause harm to the organization’s assets. The two types of risk analysis include quantitative analysis and qualitative analysis. While quantitative analysis makes use of different numbers to identify the impacts of risks, the qualitative analysis approach does not make use of any numbers and is conducted using the analysis of the technical knowledge of experts. This removes the possibility of qualitative analysis being measurable. Once an organization completes a risk analysis, it has to develop a report of the risk management plan. This report notes the efficiency of the mitigation plans implemented and any future developments that could be adopted to deal with similar occurrences in the organization.
Impacts of Risks
The occurrence of risks can lead to different impacts. Most risks likely to occur in an organization often lead to the destruction of different assets. This results in financial losses, one of the significant impacts of organisational risks. Financial losses from the exploitation of risks can occur in different ways. One of the ways is that in an attack involving intruders, the attackers might transfer funds from the organization’s accounts, leading to a loss of funds for the organization. Financial losses can also occur when different computer systems’ assets are damaged and have to be replaced. When an attack occurs, the availability of the organisation’s different services is impacted. Without operations, the organization cannot make any profits, which leads to financial losses. The occurrence of risks in the system can also result in lawsuits from the organisation’s customers for failure to protect their confidential data. Such lawsuits can lead to financial strains for the organization.
Apart from financial losses, an organization can suffer different impacts following risks in its systems. Another example of an impact of risks in an organization is the loss of intellectual property. In an organization, different forms of intellectual property are stored in the computer system. When the computer system is compromised, the intellectual property can be revealed to competitor firms, hence, reducing the competitive advantage the business might have possessed. Another impact is the loss of confidence in the organization’s operations by different stakeholders, including the organization’s customers. This can prompt customers to get services and goods from competitor firms. Another impact can arise if confidential information about the company’s employees is stored in the computer system. When the system is compromised, the confidentiality of the employees’ information is also lost. The result is that the employee would not want to be associated with an organization that cannot protect its employees’ and customers’ confidential information and would then opt to leave.
Technological Safeguards
One of the stages in risk analysis involves the identification of different controls to mitigate the risks in an organization. The controls can be implemented in different ways, and one of the ways includes the implementation of technological safeguards. An example of a technological safeguard that can be executed in an organization includes access control measures. The implementation of access control measures limits access to different areas in the workplace by requiring authentication of the individual’s identity. This can be implemented by making use of security guards, using fingerprints, and using card readers. Another security measure that can be implemented in an organization is firewalls. A firewall is a system that filters the traffic going in or out of a network using predetermined rules. The different types of firewalls include packet-filtering firewalls, circuit-level firewalls, application-level firewalls, and proxies. The packet-filtering firewalls execute the firewall rules by analyzing the contents of the packet headers, while circuit-level firewalls analyze the connection states of the packets and do not consider the information on the packet headers. The application-level firewall considers the payload of the packets. By doing this, the application-level firewall can identify malicious content that could be hidden in the payload. This makes the application-level firewall more valuable than the circuit-level and packet-filtering firewalls. A proxy firewall is an intermediary between the client and a web server. The proxy firewall then forwards the requests and replies between the client and the web server (Stallings et al., 2012).
Another safeguard that can be implemented is the use of data encryption methods. Data encryption would protect the information in the system from being useful to an attacker even when they gain access to the data. These security measures transform the information in the system into incomprehensible information, which can only be understood after decrypting the information. An organization can use different encryption methods. Examples of these methods include the Caesar Cipher Code, hashing, and public-key cryptography (Singh, 2013). Other security measures that an organization can implement include antivirus and antimalware software and audit-control software. Antivirus and antimalware software are used to identify any viruses and malware in the system and remove them. Examples of antivirus software include Avast and Kaspersky. The audit-control software produces event logs of the organization’s system. These logs can be used to identify security vulnerabilities in the system and attempt to gain unauthorized access. Examples of audit-control software include Google Analytics and Sam Spade.
While implementing security measures in an organization, the organization should consider some recommendations for implementing effective security measures. One of the recommendations is using a combination of different security measures. An example of this is the use of authorization and authentication together. Another recommendation is to consider the network users. This would help the organization implement security measures to prevent internal attacks. Another recommendation would include tamper-proof authentication methods that cannot be easily avoided.
Security Testing and Assessment
Security testing and assessment refer to how an organization can determine the efficiency of the different security measures implemented in its system. The various assessment methods include examination, interviewing, and testing (Scarfone et al., 2008). The different phases that constitute a testing and assessment method include the planning phase, the execution phase, and the post-execution phase. Conducting tests in an organization can be done from different perspectives. Examples of these perspectives include external and internal testing. In external testing, the security measures are assessed on their ability to deal with attacks outside the organization’s security. This includes assessing the different security measures, such as firewalls and protocols like Simple Mail Transfer Protocol (SMTP). Internal security testing involves testing the security measures that protect the organization’s system once the perimeter security has been compromised. The different security measures involved in this type of testing include the authentication system and access control measures.
Another perspective that can be used when conducting testing includes overt and covert security testing. In overt security testing, the individual conducting the security testing does so with authorization from the organization. In covert security testing, the individual conducting security testing is also the organization’s top management; however, unlike in overt security testing, the organization’s IT staff are not notified. While overt security testing aims at identifying the different vulnerabilities in the system, covert security testing aims at identifying the different impacts that can be caused by a threat (Scarfone et al., 2008).
Securing Wireless Networks
The different benefits of wireless networks prompt organizations to adopt their use over wired networks. The increased adoption of wireless networks also increases the vulnerabilities of the organization’s security. To address the vulnerabilities, different security measures are suggested for wireless networks. An example of these measures is Wi-Fi Protected Access (WPA2) and Wired Equivalent Privacy (WEP) to encrypt the communication between wireless computers or other devices and the wireless router. The WPA2 can also be applied to an administrator’s computer. Securing the administrator computer can also include changing the default password for the router and disabling the remote administration functionality. The router can be protected from threats by making the network name invisible. Reducing the router’s transmission power to cover only the required areas can also help protect the wireless network. Wi-Fi Protected Access (WPA2) is also recommended to encrypt data in the wireless network (Glass et al., 2008).
Other Related Post: Chapter 3 Questions
References
Anikin, I. V. (2015, May). Information Security Risk Assessment And Management Method In Computer Networks. In 2015 International Siberian Conference On Control And Communications (SIBCON) (Pp. 1-5). IEEE.
Behnia, A., Rashid, R. A., & Chaudhry, J. A. (2012). A Survey Of Information Security Risk Analysis Methods. Smarter, 2(1), 79-94.
Glass, S., Portmann, M., & Muthukkumarasamy, V. (2008). Securing Wireless Mesh Networks. IEEE Internet Computing, 12(4), 30-36.
Scarfone, K., Souppaya, M., Cody, A., & Orebaugh, A. (2008). Technical Guide To Information Security Testing And Assessment. NIST Special Publication, 800(115), 2-25.
Singh, G. (2013). A Study Of Encryption Algorithms (RSA, DES, 3DES, And AES) For Information Security. International Journal Of Computer Applications, 67(19).
Stallings, W., Brown, L., Bauer, M. D., & Bhattacharjee, A. K. (2012). Computer Security: Principles And Practice (Pp. 978-0). Upper Saddle River, NJ, USA: Pearson Education.
ORDER A PLAGIARISM-FREE PAPER HERE
We’ll write everything from scratch
Question
Project 3 instructions.
Risk Assessment Report
Project 3
There are nine steps that will help you create your final deliverables. The deliverables for this project are as follows:
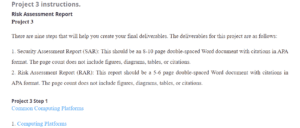
Risk Assessment Report
- Security Assessment Report (SAR): This should be an 8-10 page double-spaced Word document with citations in APA format. The page count does not include figures, diagrams, tables, or citations.
- Risk Assessment Report (RAR): This report should be a 5-6 page double-spaced Word document with citations in APA format. The page count does not include figures, diagrams, tables, or citations.
Project 3 Step 1
- Computing Platforms
- The Hardware Cloud: Utility Computing and Its Cousins
- Distributed Computing
- What is Open Source?(Recommended)
- Cloud Computing
- Data Security and Privacy in Cloud Computing
- Trusted Computing Strengthens Cloud Authentication
Secure Programming Fundamentals
- Avoiding the Top 10 Software Security Design Flaws
- Comprehensive Review on Adaptability of Network Forensics Frameworks for Mobile Cloud Computing
- Vetting the Security of Mobile Applications
- Security by Design PrinciplesRecommended
Project 3 Step 2
- Threats to Information Security
- Top 10 Considerations for Building an Insider Threat Mitigation Program
- Analysis of Insiders Attack Mitigation Strategies
- Check Your Knowledge (Test)
Project 3 Step 3
Project 3 Step 5
- Technological Safeguards
- Types of Firewalls
- Improving Network Security: Next Generation Firewalls and Advanced Packet Inspection Devices
- What is a Firewall and How Does It Work? Recommended
- Deep Packet Inspection Based on Many-Core Platform Recommended
- Iptables Essentials: Common Firewall Rules and Commands Recommended
- Creating Firewall Rules Recommended
- Network Address Translation Reference Recommended
- Guidelines on Firewalls and Firewall Policy Recommended
Project 3 Step 6
Spoofing/Cache Poisoning Attacks
- Cyber Attacks Explained: Cryptographic Attacks
- Cache Poisoning
- Spoofing Attacks on Packets and Methods For Detection and Prevention of Spoofed Packets
- Spoofing/Cache Poisoning Attacks Recommended
Denial of Service Attacks (DOS)
- A Denial of Service Resistant Intrusion Detection Architecture
- Defending Against Denial of Service Attacks (DOS) Recommended
- Session Hijacking
- Man-In-The-Middle-Attack
- State of the Art Survey on Session Hijacking Recommended
- OWASP Periodic Table of Vulnerabilities – Cookie Theft/Session Hijacking Recommended
- Cyber Attacks Explained: Cryptographic Attacks Recommended
- Practical Security Approaches against Border Gateway Protocol (BGP) Session Hijacking Attacks between Autonomous Systems Recommended
Distributed Denial of Service Attacks
Project 3 Step 8
- Risk Analysis
- Impacts of Risks
- Risks in Wireless Networks
- Intrusion Detection Using Network Monitoring Tools
- Metasploit
- Intrusion Detection System (IDS): Anomaly Detection Using Outlier Detection Approach
- Technical Guide to Information Security Testing and Assessment – Chapter 4 Recommended
- Technical Guide to Information Security Testing and Assessment – Appendix Recommended
- Technical Guide to Information Security Testing and Assessment – Chapter 2 Recommended
- IEEE Computer SocietyÈs Center for Secure Design – OWASP Recommended
- Check Your Knowledge (Test)

