Cybersecurity Policy
Introduction
A cybersecurity policy refers to standards governing the organization’s activities while interacting with the internet space. Cybersecurity policies are pertinent policies within the organization because they prevent cyberattacks and breaches that have proven to be exceedingly costly in the contemporary world (Jordan & Turnpenny, 2015). The cybersecurity policies I am collecting will primarily focus on serving the primary objective of protecting the confidential information held by the organization. It will also ensure that employees can manage the information at their disposal and prevent it from falling into the wrong hands. The policy will be arranged coherently from the definition of the security policy framework to crafting a compute incident response policy. The other policies in between would include creating a separation of duties policy, a security awareness policy, an acceptable use policy, and a security policy framework implementation policy. I chose to place the policies in this order because it necessitates easy comprehension by employees without requiring much elaboration. These policies are briefly described below;
Unit I: Defining a Security Policy Framework
A security policy framework is a set of standards, guidelines, and approaches for protecting people, information, and infrastructure.
Unit II: Creating a Separation of Duty Policy
The separation of duty policy is a logical container that tells apart rules that define mutually exclusive relationships among roles. The rules will inform the formulation of these policies. This will be composed of enabled and disabled policies. Enabled guidelines outline the exemption approvals that warn users before submitting a change in membership role (Jordan & Turnpenny, 2015). The disabled policies, on the other hand, track violations and generate approvals.
Unit III: Creating a Security Awareness Policy
A security awareness policy refers to proactive measures taken by the organization to prevent the dangers of online or offline threats from facing the organization. This policy outlines how the data belonging to the organization will be protected from internal and external threats (Craft & Howlett, 2012). Presents safety guidelines and highlights the proper steps to take when the organization finds itself in an emergency. This ensures the safety of the business, employees, and customers.
Unit IV: Creating an Acceptable Use Policy
While creating an acceptable use policy, it is essential to consider impacts before establishing rules. In this regard, the consequences of a data breach within the organization would be considered before selecting laws. Also, I will ensure that the management team is reasonable enough and allow the employees to work and use different social media platforms to deliver on their mandate. The acceptable use policy will also be informed by feedback solicited from the organization’s stakeholders.
Unit V: Developing a Security Policy Framework Implementation Plan
Developing a security policy framework implementation plan would require decision-makers to identify critical systems obligated to carry sensitive information. Furthermore, ethical standards should be integrated within the framework implementation plan, and the management should lead the course to achieve those goals and objectives. As such, an effective implementation plan will synthesize legal and regulatory concerns, organizational attributes, and environmental issues into clear goals and objectives for employees to perform (Jordan & Turnpenny, 2015).
Unit VI: Crafting a Security or Computer Incident Response Policy
The computer incident response policy’s primary objective is defining IT roles and responsibilities to attend to computer security incidents. The procedure is applied majorly to the information system of the organization concerning the location, storage, transmission, or access to the organization’s data (Craft & Howlett, 2012). The policy will work by detecting and investigating whether certain events occurred, their extent, and their respective damages. Furthermore, it also directs the recovery and remediation of security incidents. The policy is dynamic in an attempt to ensure that responses are effective in overcoming the existing challenge. To sum it up, this policy minimizes the damage caused by security threats, including but not limited to data loss, vandalism of resources, and the loss of the firm’s reputation.
References
Craft, J., & Howlett, M. (2012). Policy formulation, governance shifts, and policy influence: Location and content in policy advisory systems. Journal of Public Policy, 32(2), 79-98.
Jordan, A. J., & Turnpenny, J. R. (2015). The Tools of Policy Formulation. Actors, Capacities, Venues, and Effects.
ORDER A PLAGIARISM-FREE PAPER HERE
We’ll write everything from scratch
Question
Throughout this course, you have had an opportunity to develop several cybersecurity policies for an organization. This assignment allows you to collect each of those cybersecurity policies and insert them into one professional deliverable. You must decide in which order to place the policies. Which order makes the most sense to you? Explain the order in the introduction section. You can go back to the labs to review your text entries.
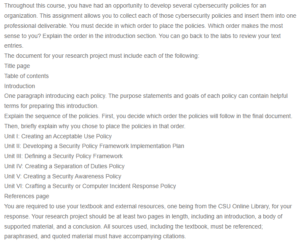
Cybersecurity Policy
The document for your research project must include each of the following:
Title page
Table of contents
Introduction
One paragraph introducing each policy. The purpose statements and goals of each policy can contain helpful terms for preparing this introduction.
Explain the sequence of the policies. First, you decide which order the policies will follow in the final document. Then, briefly explain why you chose to place the policies in that order.
Unit I: Creating an Acceptable Use Policy
Unit II: Developing a Security Policy Framework Implementation Plan
Unit III: Defining a Security Policy Framework
Unit IV: Creating a Separation of Duties Policy
Unit V: Creating a Security Awareness Policy
Unit VI: Crafting a Security or Computer Incident Response Policy
References page
You are required to use your textbook and external resources, one being from the CSU Online Library, for your response. Your research project should be at least two pages in length, including an introduction, a body of supported material, and a conclusion. All sources used, including the textbook, must be referenced; paraphrased, and quoted material must have accompanying citations.

